
While You Were Fearing Max, RuStore Was Already on Your Phone
You can choose not to install Max. RuStore is already on every phone — collecting data about your apps, geolocation, and keyboard input.

You can choose not to install Max. RuStore is already on every phone — collecting data about your apps, geolocation, and keyboard input.

I got my hands on the source code of the ERMAC 3.0 banking trojan. Here's how it steals crypto wallets, intercepts SMS messages, swaps addresses in the clipboard — and why its authors still won't land a job at any legitimate company.

Breaking down the scheme with fake crypto exchanges that promise profits from arbitrage — how the funnel works and why your money will not be returned.
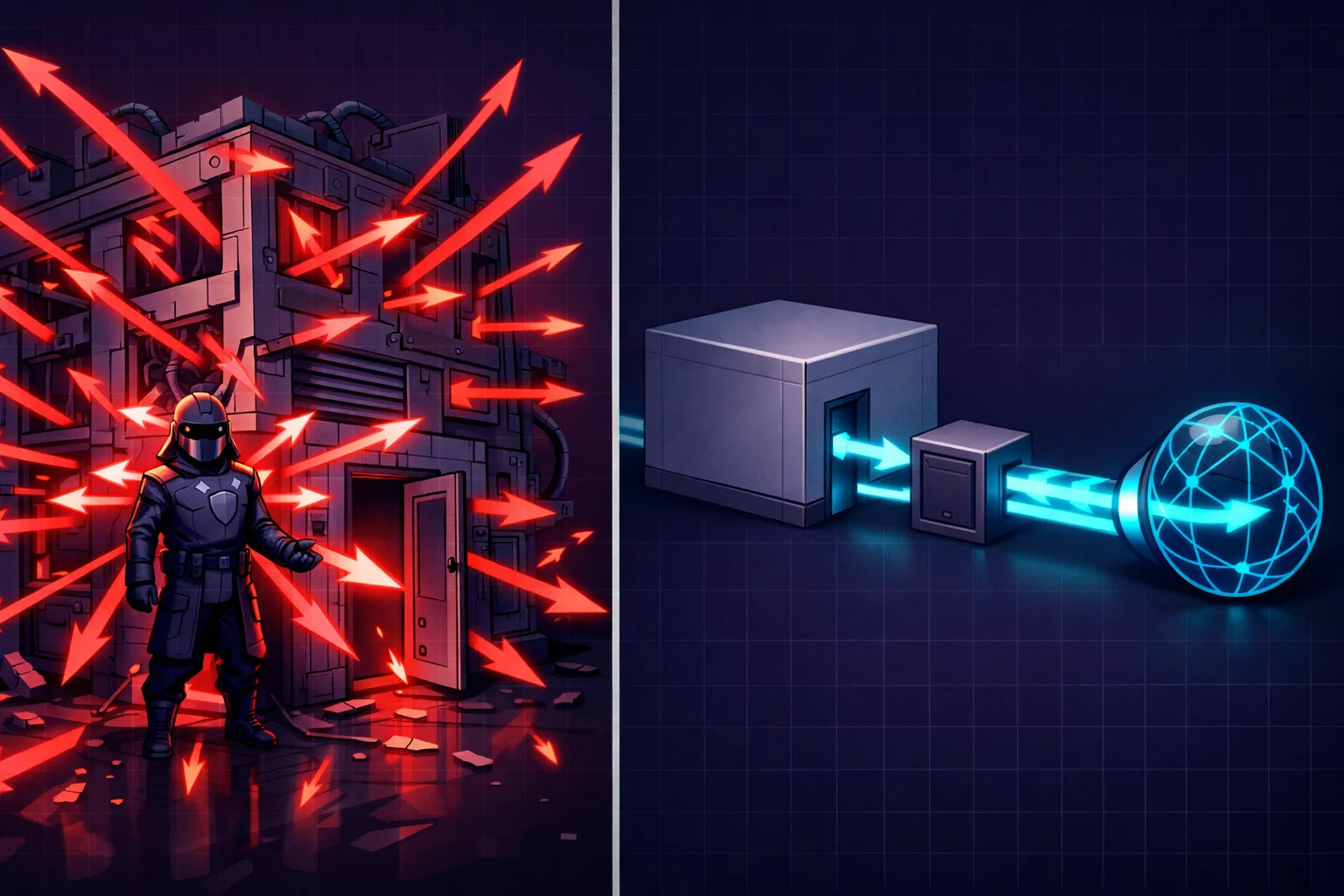
A VPN client on your computer is just software that can be bypassed. Whonix solves this through physical isolation: the workstation has no direct internet access. We break down the principle and build our own version with a fast VPN instead of Tor.

Or the story of how a bootable CD, Windows XP, and human laziness created the perfect crime